What is OWASP and why every developer should know it

Personally, I learned about OWASP when I was just starting out as a developer at PlacetoPay (now evertec) since it was a fundamental requirement for every developer to know and be familiar with security and coding best practices. Thus, a frequent training included a whole chapter dedicated to what we will see next.
What is OWASP?
OWASP (Open Web Application Security Project) is a non-profit project worldwide that seeks to improve software security in general. For this, the organization has provided itself with a series of tools and documents that explain what the most common security breaches are in any information system. Needless to say, all OWASP materials are available for free for their consultation and use.
Why is it important to know?
OWASP is a world-class organization, you will not find a larger compendium of vulnerabilities than those mentioned by OWASP so well documented. Many software development companies are aware of this, so it is not uncommon for good offers for us developers to include a component that includes knowledge of OWASP.
What are their exact contents?
Currently, OWASP actually has several projects in which Tool Projects, Code Projects, and Documentation Projects stand out. The best-known documentation project is the TOP TEN, in which the 10 most common vulnerabilities (security risks) and how to prevent them are listed. In this top, you will recognize terms like SQL INJECTION, Cross-Site Scripting (XSS), and Broken Authentication. Without further ado, I leave you with this list of ten security risks or vulnerabilities.
TOP 10 - Most Critical Web Application Security Risks
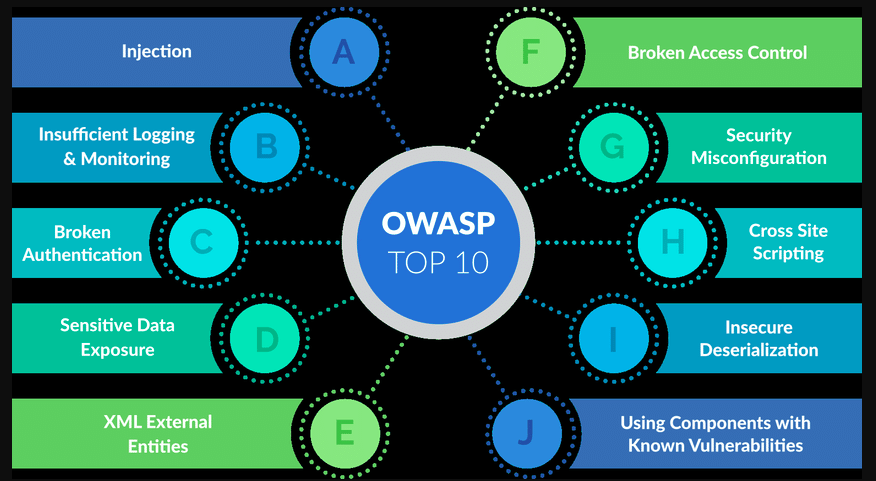
- A1: Injection
- A2: Broken Authentication
- A3: Sensitive Data Exposure
- A4-XML External Entities (XXE)
- A5-Broken Access Control
- A6-Security Misconfiguration
- A7-Cross-Site Scripting (XSS)
- A8-Insecure Deserialization
- A9: Using Known Vulnerable Components
- A10-Insufficient Logging & Monitoring